How to avoid cyber risks in the construction industry
- More than 75 percent of survey respondents in the construction, engineering and infrastructure industries experienced a cyber-incident within the previous 12 months (Forester, 2020).
- Some 74 percent of construction-related organizations are not prepared for cyberattacks and do not have an incident response plan in place.
- Learn ways to assess and address cyber risks at your construction firm.
Construction industry cyber security is a growing challenge, thanks to technological advances that range from digital design tools to everyday emails. Unfortunately, many companies have been slow to properly identify and address their cyber risk vulnerabilities.
A 2020 Forrester survey revealed that more than 75 percent of respondents in the construction, engineering and infrastructure industries had experienced a cyber-incident within the previous 12 months.
An IBM Ponemon study showed that 74 percent of construction-related organizations are not prepared for cyberattacks and do not have an incident response plan in place.
Last year, ransomware cost businesses more than $20 billion in damages; a study by Safety Detectives found that construction was the third most common industry to experience ransomware attacks in 2021 (13.2 percent of total ransomware attacks in North America).
Related: Cyber security and data protection in our new reality
Why do cybercriminals target construction firms?
Contractors, both large and small, hold vast amounts of information that’s of interest to cyber criminals, from employee data to intellectual property. Construction firms work with a variety of vendors; each transaction can involve several parties, providing ample opportunity for an internal or external bad actor to wreak havoc.
In recent years, the construction industry has increasingly implemented artificial intelligence and robotics, which, given their interconnectivity, require additional data security and privacy considerations.
In their construction industry cyber security white paper, Zurich says understanding these threats may help contractors identify vulnerabilities and better manage recovery efforts following a cyberattack.
Here’s one example Zurich noted:
Should someone gain access to the design files for a bridge under construction, changing a single measurement could drastically alter its load-bearing capacity. The organization could then be held to ransom in return for details of what the attacker has altered. The attacker may not understand the potential impact of what they have done, though in extreme cases their goal may be to cause the structural failure of the bridge.
However, ransomware – holding the company hostage for funds – isn’t the only motivating factor for many cybercriminals. The Information Systems Audit and Control Association (ISACA) reports that only half of cyberattacks are motivated by financial gain. “When you consider how many functions now have a digital element – from office payroll systems to equipment being used on site – there is an increasing number of avenues for attackers to exploit, thanks to this burgeoning Internet of Things,” says Zurich in their white paper.
Other cybercriminal motivators: Damage and interruption
Here’s another example cited by Zurich: A customer experiences a loss from a mechanical fire where a machine overcharged due to a temporary failure in the automated control system. A claim is made for physical damage and business interruption, but investigations may not extend to the root cause of the system’s temporary failure: cyber interference.
With a growing number of physical assets connected to a company’s network, there is no longer a clear dividing line between the physical and the digital. That’s why it’s important to acknowledge cyber risk’s ability to cross these barriers when managing potential risks and examining losses.
Related: Top 10 construction site safety basics
How cybercriminals discover and exploit vulnerabilities
Construction firms unknowingly offer low-hanging fruit for cybercriminals. Zurich names these common vulnerabilities in the construction industry:
- Lack of employee training
- Older operating systems
- Slow security patching
- Weak login credentials
- Physical theft on site
- Phishing scams
- Unencrypted communications
Construction industry cyber security: Protecting your company
Construction firms need to be proactive with cybersecurity, says Zurich, assessing and addressing their vulnerabilities such as
- Physical controls – for example, locking screens on unattended devices and controlling access to areas where sensitive information could potentially be accessed.
- Technical controls – for example, ensuring machines have the latest updates, security patches and encryption methods, and tools like firewalls and antivirus programs.
- Administrative controls – for example, policies and procedures, and training employees, contractors and subcontractors on their role in maintaining information security.
Even a mundane office printer may potentially open a door into an organization’s entire network. Anything that either stores data or has a connection to the outside world should be examined from a cybersecurity perspective.
Related: How to protect against a data breach, and what to do when one occurs
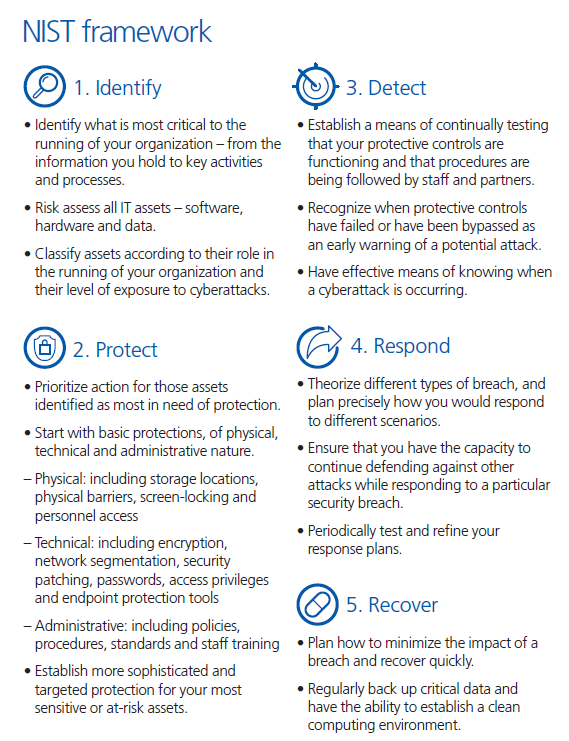
The complexity of cyber risk makes it challenging to comprehend and tackle effectively. The National Institute of Standards and Technology (NIST) has developed a helpful five-point framework. It’s a flexible and easy-to-understand template for managing cyber risk. Learn more here, www.nist.gov/cyberframework. The chart below is provided by Zurich.
Additional resources:
https://www.zurichna.com/knowledge/articles/2019/08/cybersecurity-and-the-construction-industry
https://www.aon.com/cyber-solutions/thinking/cyber-vulnerability-in-the-construction-sector/

